Learning Path 7 - Lab 1 - Exercise 1 - Modify a Microsoft Security rule
Lab scenario
You are a Security Operations Analyst working at a company that implemented Microsoft Sentinel. You must learn how to detect and mitigate threats using Microsoft Sentinel. First, you need to filter the alerts coming from Defender for Cloud into Microsoft Sentinel, by Severity.
Note: An interactive lab simulation is available that allows you to click through this lab at your own pace. You may find slight differences between the interactive simulation and the hosted lab, but the core concepts and ideas being demonstrated are the same.
Important: If you completed the previous lab Learning Path 6 - Lab 1 - Exercise 4 - Connect Defender XDR to Microsoft Sentinel using data connectors, you can skip this lab and proceed to the next exercise.
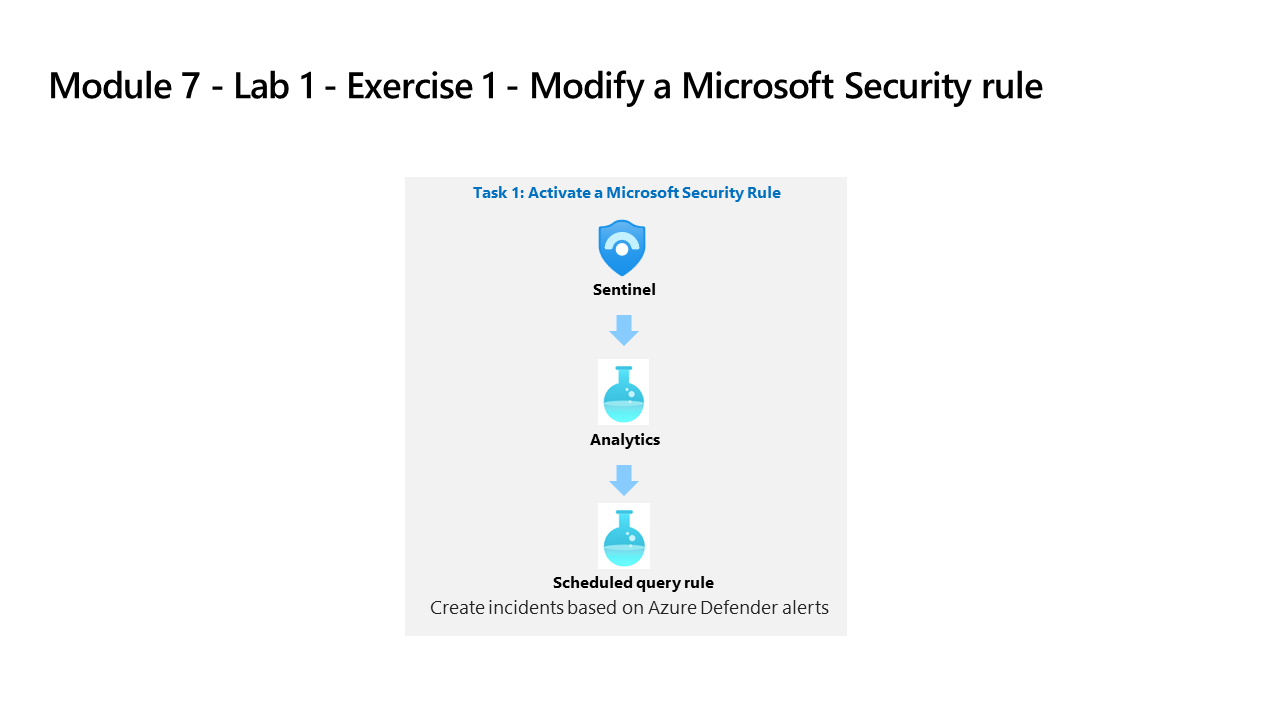
Task 1: Activate a Microsoft Security Rule
In this task, you will activate a Microsoft Security rule.
-
Log in to WIN1 virtual machine as Admin with the password: Pa55w.rd.
-
In the Microsoft Edge browser, navigate to the Azure portal at (https://portal.azure.com).
-
In the Sign in dialog box, copy, and paste in the Tenant Email account provided by your lab hosting provider and then select Next.
-
In the Enter password dialog box, copy, and paste in the Tenant Password provided by your lab hosting provider and then select Sign in.
-
In the Search bar of the Azure portal, type Sentinel, then select Microsoft Sentinel.
-
Select your Microsoft Sentinel Workspace you created in the previous labs.
-
Select Analytics from the Configuration area.
-
Select the + Create button from the command bar and select Microsoft incident creation rule.
-
Under Name, enter Create incidents based on Defender for Endpoint.
-
Scroll down and under Microsoft security service select Microsoft Defender for Endpoint.
-
Under Filter by Severity, select the Custom option and select Low, Medium and High for the severity level and go back to the rule.
-
Select the Next: Automated response button and then select the Next: Review and create button.
-
Review the changes made and select the Save button. The Analytics rule will be saved and incidents will be created if there is an Alert in Defender for Endpoint.
-
You will now have the one Fusion and two Microsoft Security alert types.